Ubuntu Firewall – Configure Ubuntu 18.04 Firewall with UFW
UFW (Ubuntu Firewall) is a simple, easy-to-use, front-end interface to manage Linux iptables firewall. Iptables rules are complicated and UFW is designed to make things less complicated for administrators, that is why it also called Uncomplicated Firewall.
In this tutorial We’ll walk through the process of enabling and configuring the UFW on Ubuntu 18.04. we’ll walk through a number of examples showing how to open ports, allow IP address, block IP address and reset firewall in Ubuntu.
Enabling and disabling Ubuntu Firewall
UFW Firewall is disabled by default on Ubuntu 18.04, so we need to enable it, but we need to do it the correct way. The correct way is, first we must add firewall rule to open ssh port 22, then we activate the firewall. If you start the firewall without opening SSH port, we won’t able to access the command line remotely.
This is how it is Done.
First, we need to add a rule that will allow us to remotely connect through SSH:
sudo ufw allow 22/tcpThen, we can activate the firewall with ufw enable command:
sudo ufw enable
Command may disrupt existing ssh connections. Proceed with operation (y|n)? y
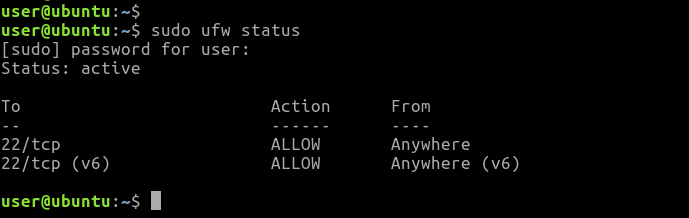
Firewall is active and enabled on system startupWe can see the status of Ubuntu firewall with following command:
sudo ufw statusAs you can see ufw is now activated, We also have firewall rules that allow incoming SSH traffic both IPv4 and IPv6.
If you want to disable Ubuntu Firewall, simply execute:
sudo ufw disableAt this point our Ubuntu server blocks all incoming traffic except for the SSH. Next, we will see how to open additional network ports on UFW.
Opening ports in UFW to allow network traffic
The ufw allow command adds allow rules to the firewall. To allow incoming traffic from a specific port we can use either service name or the port number.
If you are running a web server on your Ubuntu system, you need to allow HTTP traffic from the firewall. The following command will allow HTTP traffic from all sources:
ufw allow httpAlternately, you can use the port number in place of the name of a service:
ufw allow 80/tcpNote that we specified the protocol name when opening the port 80, because it is a TCP port. If you leave out the protocol name, ufw will open a port for both TCP and UDP protocols.
ufw allow 53The preceding rule will open DNS port 53 for both TCP and UDP protocols.
Filter network access by IP/Network
The Ubuntu UFW firewall can allow/block incoming traffic based on the client IP Address or Network. For example, following firewall rule will allow all traffic from the from the 192.168.1.10 IP Address.
ufw allow from 192.168.1.10Allow FTP traffic from the 192.168.1.0/24 network:
ufw allow from 192.168.1.0/24 to any proto tcp port 21The ufw deny command use to add deny rules. Following rule will deny all incoming traffic from 192.168.1.10 IP:
ufw deny from 192.168.1.10 to anyNote that “to any” means, to any interface on the server.
Delete Firewall rules
We can remove a rule by simply prefixing the original rule with delete option. You can list added rules as they added by running the following command:
ufw show addedFor example, if the original rule was:
ufw allow 80/tcpDelete the rule as follows:
ufw delete allow 80/tcpAlternatively, you can delete rules by specifying the rule number. To see a list of numbered rules, use:
ufw status numberedFor example, if you want to delete rule number ‘2’, Run:
ufw delete 2Resetting the Ubuntu Firewall
If you want to remove all firewall rules, run the reset command. The reset command Disables and resets firewall to installation defaults.
ufw resetUbuntu Firewall is no longer active after the reset operation:
ufw status
Status: inactiveSummary
UFW, also known as uncomplicated firewall, is the default front-end command line tool to manage iptables on Ubuntu 18.04. Ufw Firewall is disabled by default in Ubuntu 18.04 and we must open the ssh port before we enable the firewall. Otherwise, we will not be able to access the command line remotely once we exit from from the current ssh session.